This post was originally published on Security Affairs. It can be found here.
ConnectWise detected suspicious activity linked to a nation-state actor, impacting a small number of its ScreenConnect customers.
ConnectWise revealed it had detected suspicious activity linked to an advanced nation-state actor. The company confirmed that the attack impacted a small number of its ScreenConnect customers.
“ConnectWise recently learned of suspicious activity within our environment that we believe was tied to a sophisticated nation state actor, which affected a very small number of ScreenConnect customers,” the software firm said in a statement. “We have launched an investigation with one of the leading forensic experts, Mandiant. We have communicated with all affected customers and are coordinating with law enforcement. As part of our work with Mandiant, we patched ScreenConnect and implemented enhanced monitoring and hardening measures across our environment. We have not observed any further suspicious activity in any customer instances. The security of our services is paramount to us, and we are closely monitoring the situation and will share additional information as we are able.”
ConnectWise is a Florida-based software company that provides IT management solutions, including Remote Monitoring and Management (RMM), cybersecurity tools, automation software, and Business management platforms.
It’s primarily used by Managed Service Providers (MSPs) and IT departments to streamline operations, support clients, and secure IT environments.
The product ConnectWise ScreenConnect is a remote desktop and remote support software designed to enable secure, real-time access to computers and devices from anywhere. IT professionals, managed service providers (MSPs), and businesses widely use it to troubleshoot, maintain, and manage endpoints remotely.
The company launched an investigation into the incident with the help of cybersecurity firm Mandiant. ConnectWise notified all impacted clients, and is cooperating with law enforcement. The software firm patched the flaw in ScreenConnect and enhanced monitoring and security measures. Since the update, no further malicious activity has been observed. ConnectWise continues to monitor the situation closely and will share updates as available.
“We’ve seen no further activity since the patch was implemented.” a source familiar with the cyber incident, who asked for anonymity, told CRN.
ConnectWise hasn’t revealed when the breach happened or how many users were affected, but confirmed it contacted all impacted parties. The company hasn’t confirmed if any data was stolen or systems were compromised beyond unauthorized access.
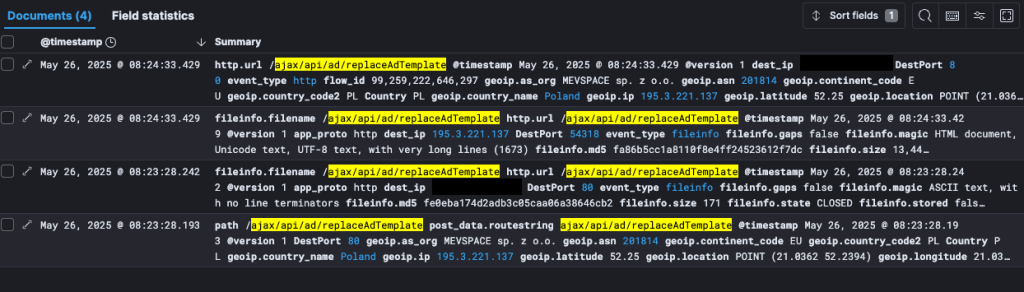
However, BleepingComputer reported that the breach may have occurred in August 2024 and the intrusion has remained undetected since May 2025.
A ScreenConnect flaw, tracked as CVE-2025-3935, may have led to a ConnectWise breach, allowing remote code execution via stolen machine keys. Though ConnectWise hasn’t confirmed if this vulnerability was exploited, it patched the issue on cloud-hosted instances before disclosure.
In early 2024, multiple threat actors started exploiting the ScreenConnect vulnerabilities, tracked as CVE-2024-1709 (CVSS score of 10) and CVE-2024-1708 (CVSS score of 8.4). Both vulnerabilities were reported on February 13, 2024, through the company vulnerability disclosure channel via the ConnectWise Trust Center.
Trend Micro confirmed that Black Basta and Bl00dy ransomware groups were actively exploiting both flaws and shared details about their attack chains.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, ScreenConnect)
This post was originally published on this site